By Eric Beach and Adam Marcus
In the previous entry in the Privacy Solutions Series, we described how privacy-sensitive users can use proxy servers to anonymize their web browsing experience, noting that one anonymizer stood out above all others: Tor, a sophisticated anonymizer system developed by the Tor Project, a 501(c)(3) U.S. non-profit venture supported by industry, privacy advocates and foundations, whose mission is to “allow you to protect your Internet traffic from analysis.” The Torbutton plug-in for Firefox makes it particularly easy to use Tor and has been downloaded over three million times. The TorBrowser Bundle is a pre-configured “portable” package of Tor and Firefox that can run off a USB flash drive and does not require anything to be installed on the computer on which it is used. Like most tools in the Privacy Solutions series, Tor has its downsides and isn’t for everyone. But it does offer a powerful tool to privacy-sensitive users in achieving a degree of privacy that no regulation could provide.
By Eric Beach & Adam Marcus
Among Internet users, there are a variety of concerns about privacy, security and the ability to access content. Some of these concerns are quite serious, while others may be more debatable. Regardless, the goal of this ongoing series is to detail the tools available to users to implement their own subjective preferences. Anonymizers (such as Tor) allow privacy-sensitive users to protect themselves from the following potential privacy intrusions:
- Advertisers Profiling Users. Many online advertising networks build profiles of likely interests associated with a unique cookie ID and/or IP address. Whether this assembling of a “digital dossier” causes any harm to the user is debatable, but users concerned about such profiles can use an anonymizer to make it difficult to build such profiles, particularly by changing their IP address regularly.
- Compilation and Disclosure of Search Histories. Some privacy advocates such as EFF and CDT have expressed legitimate concern at the trend of governments subpoenaing records of the Internet activity of citizens. By causing thousands of users’ activity to be pooled together under a single IP address, anonymizers make it difficult for search engines and other websites–and, therefore, governments–to distinguish the web activities of individual users.
- Government Censorship. Some governments prevent their citizens from accessing certain websites by blocking requests to specific IP addresses. But an anonymizer located outside the censoring country can serve as an intermediary, enabling the end-user to circumvent censorship and access the restricted content.
- Reverse IP Hacking. Some Internet users may fear that the disclosure of their IP address to a website could increase their risk of being hacked. They can use an anonymizer as an intermediary between themselves and the website, thus preventing disclosure of their IP address to the website.
- Traffic Filtering. Some ISPs and access points allocate their Internet bandwidth depending on which websites users are accessing. For example, bandwidth for information from educational websites may be prioritized over Voice-over-IP bandwidth. Under certain circumstances, an anonymizer can obscure the final destination of the end-user’s request, thereby preventing network operators or other intermediaries from shaping traffic in this manner. (Note, though, that to prevent deep packet inspection, an anonymizer must also encrypt data).
Continue reading →
Remember, remember the Fifth of November,
The Gunpowder Treason and Plot Privacy Dashboard, so hot,
I know of no reason
Why the Gunpowder Treason Privacy Dashboard
Should ever be forgot.
Sorry, I couldn’t resist, this being Guy Fawkes day (a major traditional holiday for Britons and, more recently, geeky American libertarians such as myself, who dress up as V for Vendetta for Halloween). Google’s announcement of its Privacy Dashboard (TechCrunch) is a major step forward in both informing users about what data Google has tied to their account in each of Google’s many products and in empowering users to easily manage their privacy settings for each product. If users decide they’d rather “take their ball and go home,” they can do that, too, by simply deleting their data.
Users can access the dashboard at www.google.com/dashboard (duh). Or, from the Google homepage, you just have to:
I have ranted once or twice before about the regulatory requirement that Google—a search engine—post a link to a privacy notice on its home page.
Not all computers all places may see it, but Google appears to be experimenting with a bit of javascript that leaves the page blank but for the Google image and the search field until you roll your cursor over it. But they’re leaving the privacy notice (and a copyright notice) there, probably for fear that privacy advocates will yelp about a modern-day paperwork violation.
This provides an opportunity to see the difference between a world with privacy notice regulation and one without. One is cluttered and overlawyered. The other is pure and clean and fresh.
Take a look for yourself. Which do you prefer?
This?

Or this?
I think the answer is obvious. The
only difference, mind you, is aesthetic. If Google were permitted to have a truly good looking Web site, users’ privacy would be no worse off for it because they don’t read privacy notices.
PFF summer fellow Eric Beach and I have been working on what we hope is a comprehensive taxonomy of all the threats to online security and privacy. In our continuing Privacy Solutions Series, we have discussed and will continue to discuss specific threats in more detail and offer tools and methods you can use to protect yourself.
The taxonomy is located here.
The taxonomy of 21 different threats is organized as a table that indicates the “threat vector” and goal(s) of attackers using each threat. Following the table is a glossary defining each threat and providing links to more information.Threats can come from websites, intermediaries such as an ISP, or from users themselves (e.g. using an easy-to-guess password). The goals range from simply monitoring which (or what type of) websites you access to executing malicious code on your computer.
Please share any comments, criticisms, or suggestions as to other threats or self-help privacy/security management tools that should be added by posting a comment below.
I have always regarded standard-setting organizations as serious players who take care to keep slightly boring the work of establishing uniformity in products and protocols. But a press release from the American National Standards Institute (ANSI) may cause me to reassess.
“IDSP Issues Report Calling for National Identity Verification Standard” is the release, and it’s bristling with error and malformed policy assertions. IDSP is the “Identity Theft Prevention and Identity Management Standards Panel,” an ANSI subgroup.
Take this doozy:
[T]he Intelligence Reform and Terrorism Prevention Act of 2004 (IRTPA) and the REAL ID Act of 2005 require verification of identity prior to the issuance of birth certificates and driver’s licenses / ID cards, respectively. However, the IRTPA regulations have not yet been released even in draft form and the REAL ID regulations do not provide practical guidance on how to corroborate a claim of identity under different circumstances.
Folks, REAL ID
repealed the identity security provisions in the Intelligence Reform and Terrorism Prevention Act. (It’s a good bet that regulations for a repealed law aren’t going to move out of draft form for a very long time, eh?) And REAL ID does not require verification of identity prior to issuance of birth certificates. What could that even mean?! “Hey you—little baby—let me see some ID before I issue you your birth certificate.”
The release repeats the tired mantra that 9/11 terrorists got U.S. identity documents—“some by fraud.” The 9/11 Commission dedicated three-quarters of a page to its identity recommendations—out of 400 substantive pages—and neither the commission nor anyone since has shown how denying people U.S. identity documents would prevent terrorism.
Are there needs for identity standards? Of course. And there are a lot of projects in a lot of places working on that. If an organization doesn’t know the law, and doesn’t know how the subject matter it’s dealing with functions in society, I don’t know how it could possibly be relied on to set appropriate standards.
ANSI should take a look at this subgroup and see if its work is actually competent. Judging by this press release, it’s not.
A large group of privacy advocacy groups and individuals sent a letter to the leadership of the House Homeland Security Committee today, suggesting that the role of Chief Privacy Officer at the Department of Homeland Security should be scrapped.
The DHS CPO has shown an extraordinary disregard for the statutory obligations of her office and the privacy interests of Americans. Outreach is certainly important, but the job of Chief Privacy Officer is not to provide public relations for the Department of Homeland Security. The job as defined in the statute is to protect the privacy of American citizens, through investigation and oversight. If an internal office cannot achieve this, then the situation calls for an independent office that can truly evaluate these programs and make recommendations in the best interests of the American public.
The current CPO, Mary Ellen Callahan, has not been on the job long enough to lay all these concerns at her feet, but the substance of the complaint is valid. Does the Privacy Office actually help protect privacy, or has it, over years, favored the paperwork function over privacy protection, falling into the role of apologist for DHS programs?
I serve on the DHS Privacy Committee, which advises the CPO. The views stated here, of course, are my own.
I wrote on Privacilla in 2001: “As a management matter, government privacy officers may become antagonistic to the agencies with whom they deal, and lose effectiveness, or they may be captured by agencies and become professional apologists for government erosion of privacy.”
And when I joined the committee four years later, I expressed my concern with the potential for co-option, saying in a Privacilla press release: “I have asked friends and family members to beat me up if I change or mute my advocacy for privacy, civil liberties, and freedom.”
Progress Snapshot 5.10
from
The Progress & Freedom Foundation
A recent telephone poll conducted by professors at Berkeley and the University of Pennsylvania concluded, “Contrary to what many marketers claim, most adult Americans (66%) do not want marketers to tailor advertisements to their interest.” The study’s authors claim that their poll is the “the first nationally representative telephone (wireline and cell phone) survey to explore Americans’ opinions about behavioral targeting by marketers.” They also assert that the poll indicates that “if Americans could vote on behavioral targeting today, they would shut it down.” Advocates of regulating online data collection have trumpeted this poll as evidence consumers demand legislation to protect their privacy. “This research gives the F.T.C. and Congress a political green light to go ahead and enact effective, but reasonable, rules and policies,” declared Jeff Chester, a leading critic of online advertising.
But what is most surprising about this poll is not that 66% of users said they do not want tailored online ads, but that 34% of users said they did! The key, initial question of “whether or not you want the websites you visit to show you ads that are tailored to your interests,” presents no trade-off. The fact that
anyusers said “yes” indicates that many users paused to do the rough mental math about the unarticulated trade-off between the benefits of receiving tailored ads and the costs of that tailoring.
The methodology of opinion polls necessarily affects respondents’ mental calculations, rendering polls not just easily manipulated, but inherently unreliable as indicators of real preferences. Every poll reflects the bias of its authors to some degree by the way questions are worded, the order in which they are asked, the sample surveyed,
etc. The easiest way to bias the results of a poll is to omit any mention of the trade-offs at issue. This poll simply buried the issue of trade-offs in a heavily loaded follow-up question: After telling respondents that marketers “often use technologies to follow the websites you visit and the content you look at in order to better customize ads,” the interviewer asked whether the respondent would allow advertisers to “follow [them] online in an anonymous way in exchange for free content.” Only 10% of users said they would allow this voluntary exchange.
What does this tell us about whether, and how, government should further regulate online advertising? Precious little: Not only does this poll overstate the costs of targeted advertising, understate its benefits, and ignore the tools available to users to address their privacy concerns but, like any opinion poll, this one tells us more about the psychology of decision-making under the artificial uncertainty of polls than about the choices users would actually make in the real world. Continue reading →
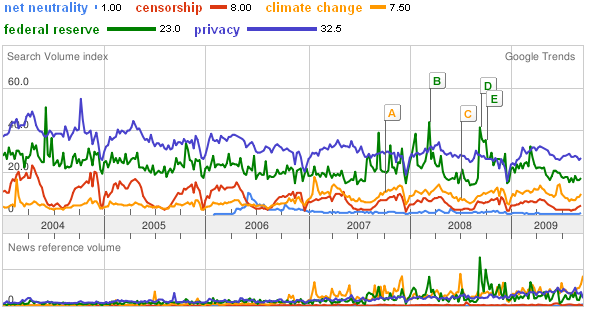
Those who advocate regulating Internet service providers as common carriers subject to “open access” mandates (a/k/a “Net Neutrality”) want us to believe that their cause is the “Civil Rights” issue of the digital age, with huge popular support and opposed only by self-interested cable companies and their henchmen. In fact, such regulations would actually harm consumers, increase broadband prices, retard the heretofore-explosive growth of bandwidth, and dramatically increase government control over the Internet. Of course, the degree of public interest in a cause doesn’t actually tell us anything about its justice and, fortunately, we live in a democratic oligarchic republic, not a pure democracy. But it’s worth asking whether Americans are really up in arms about the need for “Net Neutrality” regulations. Google Trends suggests not:
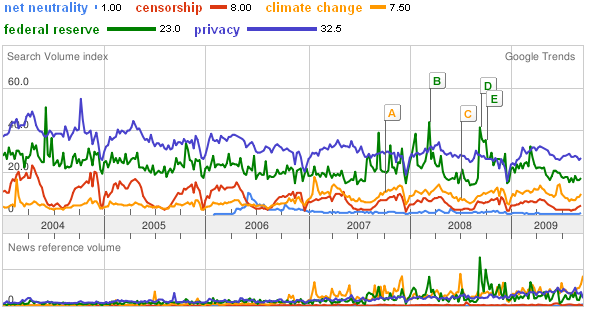 This kind of comparison should dispel once and for all the myth of a popular groundswell for net neutrality regulation—especially since online search volumes heavily over-represent the interests of the digerati, thus over-stating general interest in web-related topics.
This kind of comparison should dispel once and for all the myth of a popular groundswell for net neutrality regulation—especially since online search volumes heavily over-represent the interests of the digerati, thus over-stating general interest in web-related topics.
In fact, “Net Neutrality” regulation is a
niche cause trumpeted incessantly by the blogosphere with about the same level of broad popular interest online as “housing rights”—a topic about which most of us probably don’t often fall into conversation (unless we happen to live in Bakuninist Berkeley or the Bolivarian Caliphate of Cambridge, MA, ground-zero of American Chavismo). Continue reading →


 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.