 It’s not often that you see advice on Internet privacy sandwiched between articles on “4 Times it Pays to Splurge” and how to “Be a Full-time Mom with a Part-time Passion.” But online privacy is such a hot topic that even Redbook, the women’s magazine, has a story in its August issue. The article is an informed, well-balanced look at providing practical tips (well it should be, I was interviewed for it!) on being secure and private when on various Internet sites:
It’s not often that you see advice on Internet privacy sandwiched between articles on “4 Times it Pays to Splurge” and how to “Be a Full-time Mom with a Part-time Passion.” But online privacy is such a hot topic that even Redbook, the women’s magazine, has a story in its August issue. The article is an informed, well-balanced look at providing practical tips (well it should be, I was interviewed for it!) on being secure and private when on various Internet sites:
If you’re a LIVE-LIFE-OUT-LOUD GIRL (i.e., you offer a play-by-play of your life to your 1,000 Facebook friends, blog readers, and Twitter followers), these are the guidelines you — and everyone — should follow:
- On your social networking profiles, take the time to check out the privacy settings and decide whom you want to have access to what information. The risks here aren’t great, but do you really want your cousins to read about your sex life, or your frenemy to see photos of the party you didn’t invite her to?
- If you’re on a public wireless network, like at Starbucks, don’t do your online banking or log on to other sites that contain sensitive information about you. Other users accessing the network might be able to access it.
- Teach your kids about the risks of sharing personal information on the Web. If it feels appropriate for your child, bring up the countless cases of tweens’ and teens’ personal photos and videos that have ended up in the wrong inboxes because of how easy it is to forward email. Have a conversation about what sites they’re visiting online, and make sure they’re staying safe by signing up for a free limiting service such as AOL Parental Controls, which allows you to log in and monitor their activity. Check with your wireless carrier for similar services on your kids’ phones, too.
There’s more tips if interested, or read about unboring veggies sides for grilled food.
In reaction to recent government pressures for RIM to reveal customer encryption keys, Steve DelBianco writes over at the NetChoice blog: enough with the bullies from UAE and Saudi Arabia kicking sand on the skinny Canadian guy.
It’s not likely that the UAE and Saudi governments will pick a fight with every company in a global industry. Nor is it likely they would ban all electronic messaging, knowing their monarchs would be forced to back down after a few days of embarrassing international criticism.
It’s time for these governments to stop bullying a company that’s investing heavily to bring connectivity, content, and commerce to their own citizens. It will only lead to a larger fight where everyone loses.
Kicking sand, indeed.
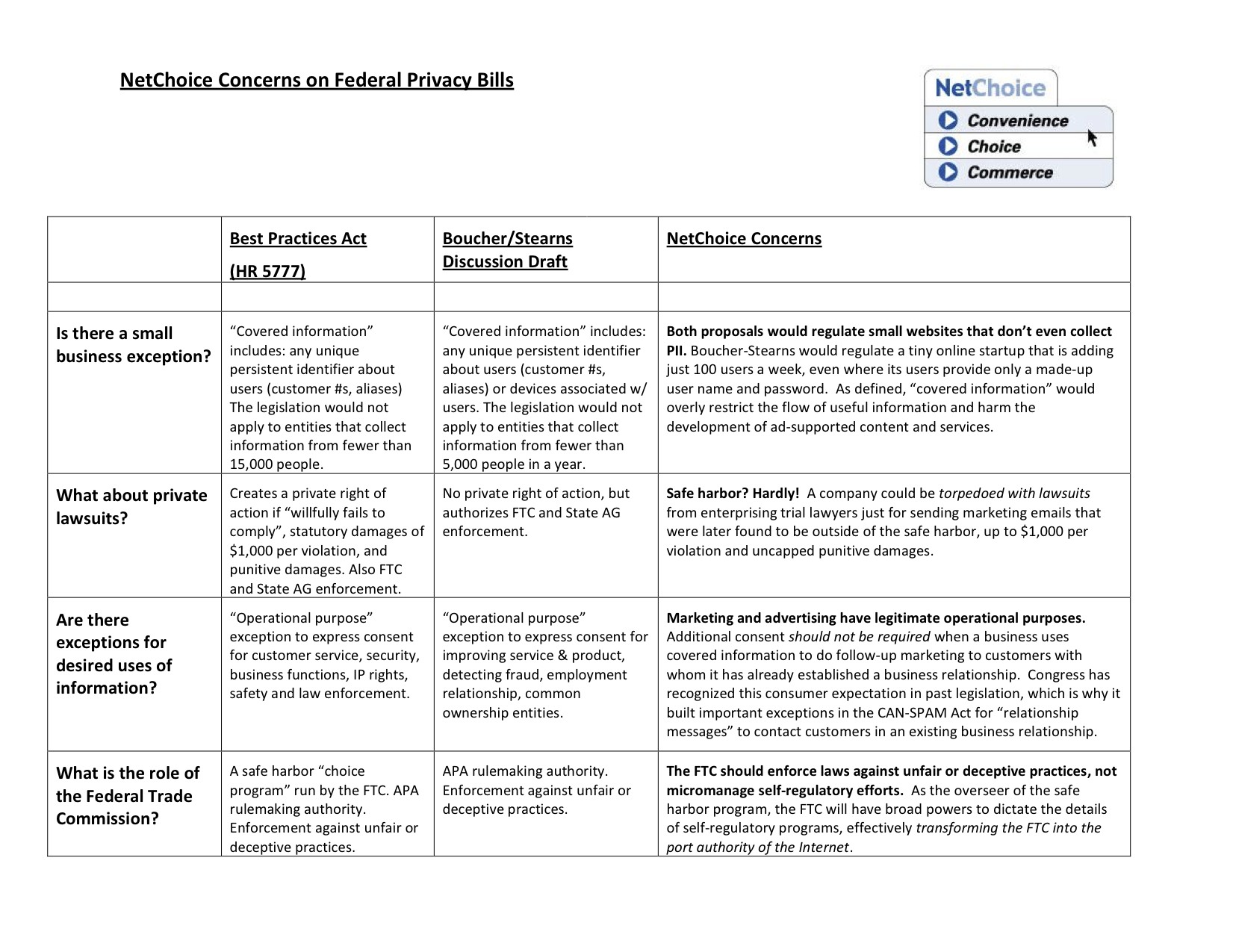
Two privacy bills are already up for consideration. And at yesterday’s Senate Commerce hearing on Consumer Online Privacy, we heard Senator Kerry announce that he will be working on new legislation to regulate online privacy. While we wait to see what Kerry will offer, NetChoice has concerns over the bills we do know about: Rep. Rush’s “Best Practices Act” and the Boucher/Stearns Discussion Draft. Our side-by-side comparison identifies four concerns: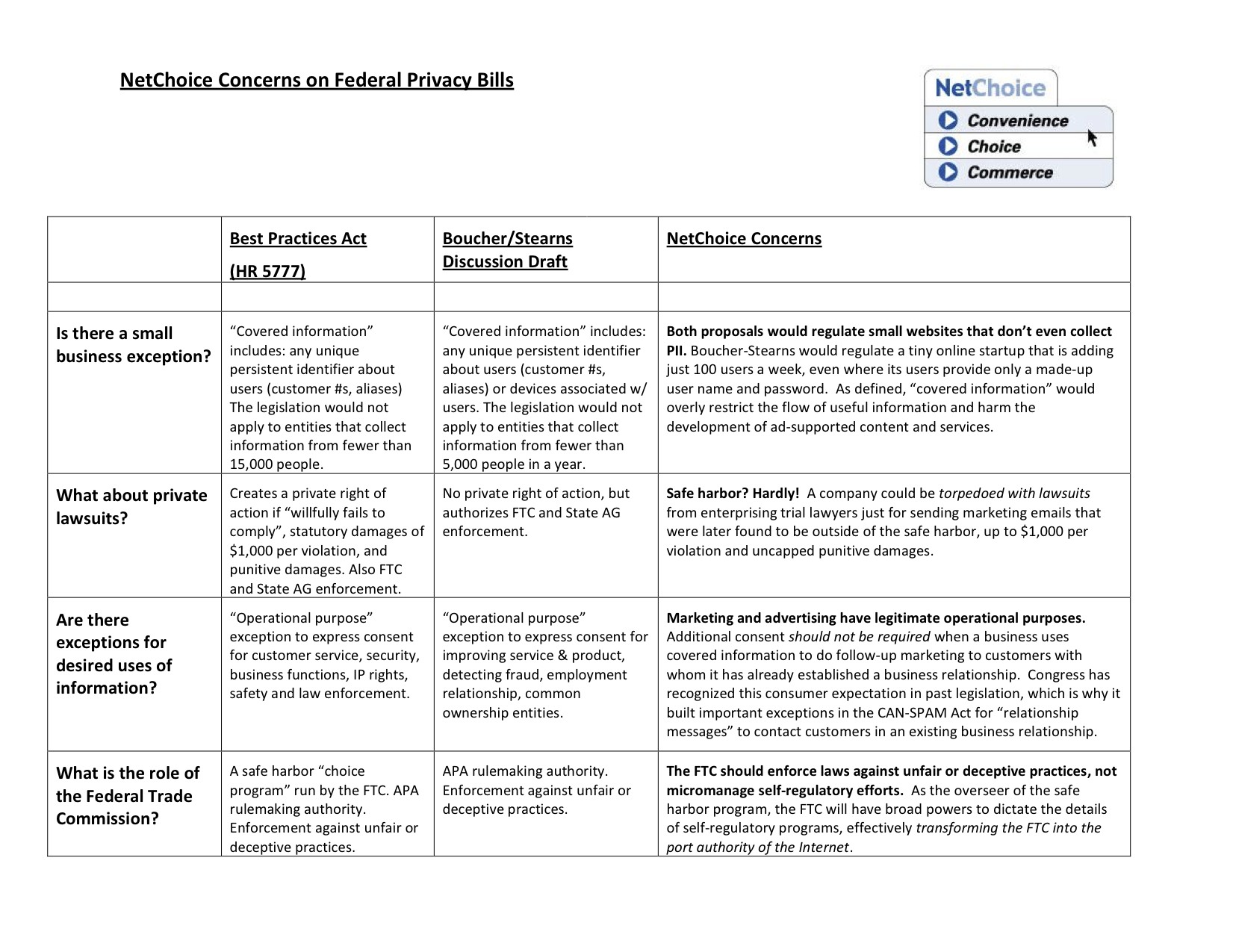
- Both proposals would regulate small websites that don’t even collect PII. Boucher-Stearns would regulate a tiny online startup that is adding just 100 users a week, even where its users provide only a made-up user name and password. As defined, “covered information” would overly restrict the flow of useful information and harm the development of ad-supported content and services. Continue reading →
The Senate Commerce Committee will hold yet another hearing today (7/27/10) at 2:30pm Eastern with two panels:
- Witness Panel 1
- FTC Chairman Jon Leibowitz
- FCC Chairman Julius Genachowski
- Witness Panel 2
- Guy “Bud” Tribble, Apple’s VP for Software Technology
- Bret Taylor, Facebook CTO
- Alma Whitten, Google’s Privacy Engineering Lead
- Jim Harper, Cato Institute
- Dorothy Atwood, AT&T’s Senior Vice President, Public Policy & Chief Privacy Officer
- Prof. Joe Turow, University of Pennsylvania
Join me to watch the livecast. I’ll be livetweeting on the #Privacy hashtag.
I summed up most of my thoughts on the online privacy issue in my written testimony to the FTC’s privacy roundtable last fall. Also check out my paper Privacy Polls v. Real-World Trade-Offs, which explains why Prof. Turow’s polls can’t really show us what choices consumers would make if actually presented with the trade-off between locking down on the use of their data and the content and services supported by advertising that relies on that data for its value.
If I ever had any hope of “keeping up” with developments in the regulation of information technology—or even the nine specific areas I explored in The Laws of Disruption—that hope was lost long ago. The last few months I haven’t even been able to keep up just sorting the piles of printouts of stories I’ve “clipped” from just a few key sources, including The New York Times, The Wall Street Journal, CNET News.com and The Washington Post.
I’ve just gone through a big pile of clippings that cover April-July. A few highlights: In May, YouTube surpassed 2 billion daily hits. Today, Facebook announced it has more than 500,000,000 members. Researchers last week demonstrated technology that draws device power from radio waves.
Continue reading →
 Check out national security reporter Shaun Waterman’s report on lapses in security using techniques that only recently became known as “social engineering.”
Check out national security reporter Shaun Waterman’s report on lapses in security using techniques that only recently became known as “social engineering.”
Ms. Sage’s connections invited her to speak at a private-sector security conference in Miami, and to review an important technical paper by a NASA researcher. Several invited her to dinner. And there were many invitations to apply for jobs.
“If I can ever be of assistance with job opportunities here at Lockheed Martin, don’t hesitate to contact me, as I’m at your service,” one executive at the company told her.
Then there’s former DHS policy official Stewart Baker’s unusually harsh attack on the “privacy lobby” and Wired reporter Ryan Singel at Volokh.com. The comments are good-quality and interesting.
Knowing how canny Baker is, I would guess that his unusually shrill tone is a ploy to start a fight that helps him sells more copies of his book. But maybe he’s just losing his cool.
Adam and I have been pretty hard on the FTC’s current leadership for pushing to dramatically expand regulation of online data use with little thought to the impact on ad-supported media, while in the next breath opening the door to dramatic expansion of direct government support of media, and all the while seeking sweeping new regulatory powers from Congress.
After all that complaining (and bashing their Soviet Realist-style statue, “Man Controlling Trade”), you might think we had it in for the agency. But as I’ve said repeatedly, we’re actually big fans of the FTC’s core consumer protection mission: holding companies to their promises. (Indeed, we want to make sure they stay focused on that mission, and have the staff, resources and technological tools to pursue it effectively—which might mean, as I’ve pointed out, increased funding rather than increased powers.) We’ve also repeatedly praised the FTC’s efforts to educate kids, parents, and Internet users in general about things like online privacy, advertising, spyware, user empowerment tools, online scams, etc.
But I don’t want to be accused of being only a fair-weather friend of the agency. So I wanted to point out a particularly good concrete example of the FTC doing what we talk about in the abstract: holding companies to their promises. Grant Gross notes that the FTC sent a stern letter earlier this month to the company that is seeking to buy the subscriber info and photos and other assets of the now-defunct XY Magazine, which served primarily gay U.S. teens, warning them that the FTC would hold them to the terms of the privacy policy under which XY collected information from its subscribers.
This is a great example of how the FTC can effectively use its existing authority to protect consumers against clear harms involved in the disclosure of truly sensitive data, sometimes even prophylactically—in this case, outing around 100,000 gay youths and young adults—collected by companies that make unambiguous promises to protect users’ data. This incident also illustrates how privacy law can evolve in an organic fashion from a growing body of such well-justified preemptive warnings, enforcement actions brought against truly bad actors, and ultimately court decisions that decide whether the FTC has properly weighed the interests at stake. In other words, just because we don’t have a privacy code enforced by a Data Protection Authority as in Europe doesn’t mean our legal system doesn’t protect privacy!
Continue reading →
 Better late than never, I’ve finally given a close read to the Notice of Inquiry issued by the FCC on June 17th. (See my earlier comments, “FCC Votes for Reclassification, Dog Bites Man”.) In some sense there was no surprise to the contents; the Commission’s legal counsel and Chairman Julius Genachowski had both published comments over a month before the NOI that laid out the regulatory scheme the Commission now has in mind for broadband Internet access.
Better late than never, I’ve finally given a close read to the Notice of Inquiry issued by the FCC on June 17th. (See my earlier comments, “FCC Votes for Reclassification, Dog Bites Man”.) In some sense there was no surprise to the contents; the Commission’s legal counsel and Chairman Julius Genachowski had both published comments over a month before the NOI that laid out the regulatory scheme the Commission now has in mind for broadband Internet access.
Chairman Genachowski’s “Third Way” comments proposed an option that he hoped would satisfy both extremes. The FCC would abandon efforts to find new ways to meet its regulatory goals using “ancillary jurisdiction” under Title I (an avenue the D.C. Circuit had wounded, but hadn’t actually exterminated, in the Comcast decision), but at the same time would not go as far as some advocates urged and put broadband Internet completely under the telephone rules of Title II.
Continue reading →
. . . when you realize how much data it can give up to law enforcement and phone thieves. Or maybe one of you smarties will write an app that wipes your iPhone clean, restoring your control over personal and private communications information.
Today, China renewed Google’s license to do business in the country, reports The Washington Post. The announcement means that Google will maintain its presence in the country for the foreseeable future. Google will likely meet criticism, but this is good news nonetheless for Chinese Internet users.
The rapidly unfolding Google-China saga has made headline after headline since January, when Google announced that it had suffered an intrusion originating in China. In March, after months of internal debate and heavy public criticism, Google shut down its China-based search engine Google.cn, redirecting all queries to its Hong Kong-based Google.com.hk site. Late last month, Google reactivated some of its China-based services and has continued to operate in China, albeit on a limited basis.
Operating in China has long been a headache for Google, due to the Chinese government’s notorious disregard for Internet freedom, embodied by its infamous “Great Firewall of China.” China surveils all Internet traffic that traverses its borders and attempts to block its citizens from accessing information sources which the government considers unfavorable. China also gleans data from its network to identify and retaliate against political dissidents.
Human rights advocates have long derided Google and other U.S. tech companies, such as Microsoft and Yahoo, for doing business in China. China requires all search engines operating in the country to censor a broad range of information, like photos of the 1989 Tiananmen Square massacre. Critics contend that complying with the Chinese government’s oppressive demands is unethical and that facilitating censorship and suppression is morally unacceptable on its face.
Such criticisms, however principled, miss the forest for the trees. If Google were to cease its Chinese operations entirely, the result would be one less U.S. Internet firm accessible to Chinese citizens. While Google is the worldwide search leader, in the Chinese search market Google lags behind Baidu, a search company based in China. Baidu’s market share increased after Google shut down its China-based search site. If Google were to pull out of China entirely, chances are Baidu would pick up many more users.
Continue reading →
 It’s not often that you see advice on Internet privacy sandwiched between articles on “4 Times it Pays to Splurge” and how to “Be a Full-time Mom with a Part-time Passion.” But online privacy is such a hot topic that even Redbook, the women’s magazine, has a story in its August issue. The article is an informed, well-balanced look at providing practical tips (well it should be, I was interviewed for it!) on being secure and private when on various Internet sites:
It’s not often that you see advice on Internet privacy sandwiched between articles on “4 Times it Pays to Splurge” and how to “Be a Full-time Mom with a Part-time Passion.” But online privacy is such a hot topic that even Redbook, the women’s magazine, has a story in its August issue. The article is an informed, well-balanced look at providing practical tips (well it should be, I was interviewed for it!) on being secure and private when on various Internet sites:
 Check out national security reporter Shaun Waterman’s
Check out national security reporter Shaun Waterman’s 

 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.