Every lover of liberty and the Constitution should be offended by the moniker “Privacy Bill of Rights” appended to regulatory legislation Senators John Kerry (D-MA) and John McCain (R-AZ) introduced yesterday. As C|Net’s Declan McCullagh points out, the legislation exempts the federal government and law enforcement:
[T]he measure applies only to companies and some nonprofit groups, not to the federal, state, and local police agencies that have adopted high-tech surveillance technologies including cell phone tracking, GPS bugs, and requests to Internet companies for users’ personal information–in many cases without obtaining a search warrant from a judge.
The real “Privacy Bill of Rights” is in the Bill of Rights. It’s the Fourth Amendment.
It takes a lot of gall to put the moniker “Privacy Bill of Rights” on legislation that reduces liberty in the information economy while the Fourth Amendment remains tattered and threadbare. Nevermind “reasonable expectations”: the people’s right to be secure against unreasonable searches and seizures is worn down to the nub.
Senators Kerry and McCain should look into the privacy consequences of the Internal Revenue Code. How is privacy going to fare under Obamacare? How is the Department of Homeland Security doing with its privacy efforts? What is an “administrative search”?
McCullagh was good enough to quote yours truly on the new effort from Sens. Kerry and McCain: “If they want to lead on the privacy issue, they’ll lead by getting the federal government’s house in order.”
San Francisco’s Entertainment Commission will soon be considering a jaw-dropping attack on privacy and free assembly. Here are some of the rules the Commission may adopt for any gathering of people expected to reach 100 or more:
3. All occupants of the premises shall be ID Scanned (including patrons, promoters, and performers, etc.). ID scanning data shall be maintained on a data storage system for no less than 15 days and shall be made available to local law enforcement upon request.
4. High visibility cameras shall be located at each entrance and exit point of the premises. Said cameras shall maintain a recorded data base for no less than fifteen (15 days) and made available to local law enforcement upon request.
Would you recognize a police state if you lived in one? How about a police city? The First Amendment right to peaceably assemble takes a big step back when your identity data and appearance are captured for law enforcement to use at whim simply because you showed up. (ht: PrivacyActivism.org)
This morning, the U.S. Senate Judiciary Committee heard key administration officials testify about the statute that governs law enforcement access to private information held electronically by third parties. Several leading lawmakers are currently working to bring this law—the 1986 Electronic Communications Privacy Act (ECPA)—into the information age so that it reflects Americans’ reasonable privacy expectations in the era of webmail, mobile services, cloud computing and the like.
TechFreedom has led, in conjunction with the Competitive Enterprise Institute and Americans for Tax Reform‘s Digital Liberty Project, a coalition of leading free market public interest in a letter to the committee voicing their strong support for overhauling the quarter-century-old ECPA. The coalition—also including FreedomWorks, the Campaign for Liberty, the Washington Policy Center, Liberty Coalition, the Center for Financial Privacy and Human Rights, and Less Government—is urging Congress to extend traditional Fourth Amendment protections to Internet-based “cloud” and mobile location services while preserving the building blocks of law enforcement investigations.
The coalition letter explains that framers of the Bill of Rights ratified the Fourth Amendment to protect individuals from unreasonable, unwarranted searches and seizures by government officials. But since courts have not consistently applied these Constitutional protections to private information stored with cloud and mobile providers, many Americans’ private information is vulnerable to warrant-less access by law enforcement. To remedy this, the letter proposes four reforms to ECPA that would resolve legal ambiguities and affirm Constitutional protections by establishing electronic privacy standards that are consistent with the Fourth Amendment.
“Major decisions regarding the future architecture of cloud computing are being made right now,” explains the letter, calling for urgent action. “If Congress fails to enact ECPA reform, cloud computing services may be designed to rely on servers outside the U.S. Not only would this harm U.S. competitiveness, it could also, ironically, deny U.S. law enforcement access to cloud data—even with a lawful warrant.”
Read the full coalition letter here or below. Continue reading →
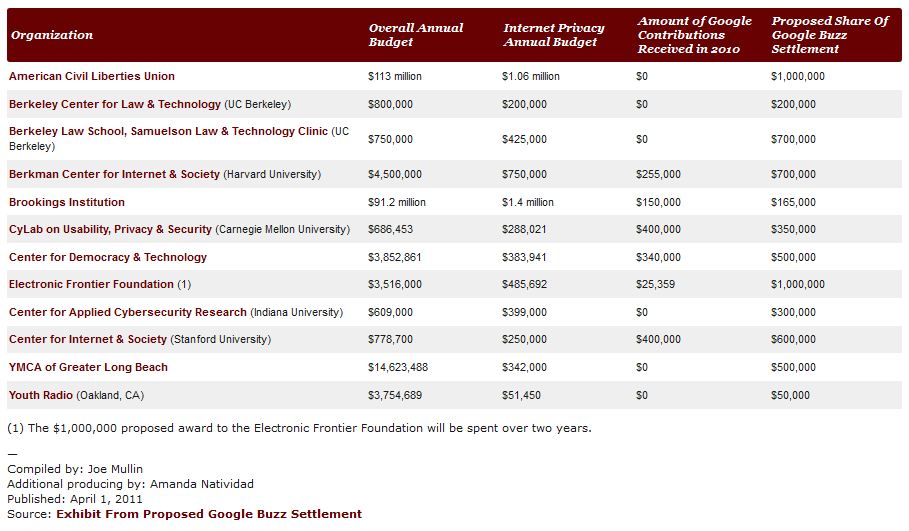
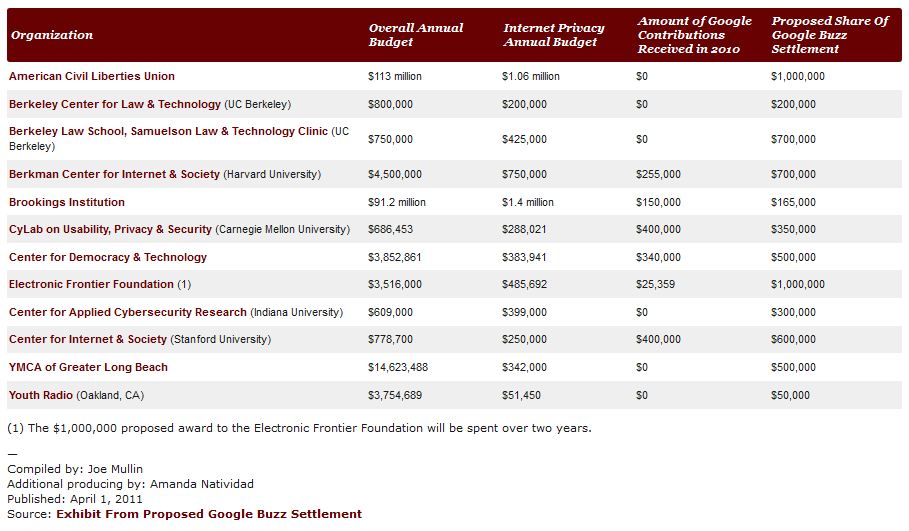
PaidContent.org has posted a chart showing “Who’s Getting Buzz Settlement Money.” This refers to the $9.5 million payout following the Federal Trade Commission settlement with Google a class action suit over its “Buzz” social networking service. Last week, the Federal Trade Commission entered into a consent decree with Google over its botched rollout of Buzz saying the search giant violated its own privacy policy. Google will also pay out to various advocacy groups according to the distribution seen in the chart as part of a separate class action. Payouts to advocates like this are not uncommon, although they are more often the result of a class action settlement than a regulatory agency consent decree. [Update/Correction 5:13 pm: I should have made it clear that this payout was the result of a class action lawsuit against Google and not the direct result of the FTC settlement. Apologies for that mistake, but still interested in the questions raised below.]
But that got me wondering whether this might make for good fodder for a case study by a public choice economist or political scientist. There are some really interesting questions raised by settlements like this that would be worth studying.
Continue reading →
I’ve posted a long article on Forbes.com this morning on the Global Network Initiative. A non-profit group aimed at improving human rights though the agency of information technology companies, GNI has never really gotten off the ground.
Since its formal launch in 2008, following two years of negotiations among tech companies, human rights groups and academics, not a single company has agreed to join beyond the original members–Google, Yahoo and Microsoft.
This despite considerable pressure from supporters of GNI, including Senator Richard Durbin (D-IL), Chair of the Senate Judiciary’s Subcommittee on Human Rights. Indeed, in the wake of uprisings in Tunisia, Egypt, Libya and elsewhere and the seminal role played by social media and other IT, a full-court press has been launched against Facebook and Twitter in particular for failing to sign up. Continue reading →
The FTC today announced it has reached a settlement with Google concerning privacy complaints about how the company launched its Buzz social networking service last year. The consent decree runs for a standard twenty-year term and provides that Google shall (i) follow certain privacy procedures in developing products involving user information, subject to regular auditing by an independent third party, and (ii) obtain opt-in consent before sharing certain personal information. Here’s my initial media comment on this:
For years, many privacy advocates have insisted that only stringent new regulations can protect consumer privacy online. But today’s settlement should remind us that the FTC already has sweeping powers to punish unfair or deceptive trade practices. The FTC can, and should, use its existing enforcement powers to build a common law of privacy focused on real problems, rather than phantom concerns. Such an evolving body of law is much more likely to keep up with technological change than legislation or prophylactic regulation would be, and is less likely to fall prey to regulatory capture by incumbents.
I’ve written in the past about how the FTC can develop such a common law. If the agency needs more resources to play this role effectively, that is what we should be talking about before we rush to the assumption that new regulation is necessary. Anyway, a few points about Part III of the consent decree, regarding the procedures the company has to follow:
- The company has to assess privacy risks raised by new products as well as existing products, much like data security assessments currently work. The company would have to assess, document and address privacy risks—and then subject those records to inspection by the independent auditor, who would determine whether the company has adequately studied and dealt with privacy risks.
- Google is agreeing to implement a version of Privacy by Design, in that the company will do even more to bake privacy features into its offerings.
- This is intended to avoid instances where the company makes a privacy blunder because it lacked adequate internal processes to thoroughly vet new offerings or simply to avoid innocent mistakes—as with the its inadvertent collection of content sent over unsecured Wi-Fi hotspots because the engineer designing its Wi-Fi mapping program mistakenly left that code in the system, even though it wasn’t necessary for what Google was doing. I wrote more on that here.
As to Part II of the consent decree, express affirmative consent for changes in the sharing of “identified information”: It’s well-worth reading Commissioner Rosch’s concurring statement. Continue reading →
Here’s an interesting SmartPlanet interview with Paul Ohm, associate professor of law at the University of Colorado Law School, in which he discusses his concerns about “reidentification” as it relates to privacy issues. “Reidentification” and “de-anonymization” fears have been set forth by Ohm and other computer scientists and privacy theorists, who suggest that because the slim possibility exists of some individuals in certain data sets being re-identified even after their data is anonymized, that fear should trump all other considerations and public policy should be adjusted accordingly (specifically, in the direction of stricter privacy regulation / tighter information controls).
I won’t spend any time here on that particular issue since I am still waiting for Ohm and other “reidentification” theorists to address the cogent critique offered up by Jane Yakowitz in an important new study that I discussed here last week. Once they do, I might have more to say on that point. Instead, I just wanted to make some brief comments on one particular passage from the Ohm interview in which he outlines a bold new standard for privacy regulation:
We have 100 years of regulating privacy by focusing on the information a particular person has. But real privacy harm will come not from the information they have but the inferences they can draw from the data they have. No law I have ever seen regulates inferences. So maybe in the future we may regulate inferences in a really different way; it seems strange to say you can have all this data but you can’t take this next step. But I think that’s what the law has to do.
This is a rather astonishing new legal standard and there are two simple reasons why, as Ohm suggests, “no law… regulates inferences” and why, in my opinion, no law should. Continue reading →
In the latest example of big government run amok, several politicians think they ought to be in charge of which applications you should be able to install on your smartphone.
On March 22, four U.S. Senators sent a letter to Apple, Google, and Research in Motion urging the companies to disable access to mobile device applications that enable users to locate DUI checkpoints in real time. Unsurprisingly, in their zeal to score political points, the Senators—Harry Reid, Chuck Schumer, Frank Lautenberg, and Tom Udall—got it dead wrong.
Had the Senators done some basic fact-checking before firing off their missive, they would have realized that the apps they targeted actually
enhance the effectiveness
of DUI checkpoints while reducing their intrusiveness. And had the Senators glanced at the Constitution – you know, that document they swore an oath to support and defend – they would have seen that sobriety checkpoint apps are almost certainly protected by the First Amendment.

While Apple has stayed mum on the issue so far, Research in Motion quickly yanked the apps in question. This is understandable; perhaps RIM doesn’t wish to incur the wrath of powerful politicians who are notorious for making a public spectacle of going after companies that have the temerity to stand up for what is right.
Google has refused to pull the DUI checkpoint finder apps from the Android app store, reports Digital Trends. Google’s steadfastness on this matter reflects well on its stated commitment to free expression and openness. Not that Google’s track record is perfect on this front – it’s made mistakes from time to time – but it’s certainly a cut above several of its competitors when it comes to defending Internet freedom. Continue reading →
FTC Commissioner J. Thomas Rosch puts the brakes on some of the Do-Not-Track excitement that has been bubbling up in this (wouldn’t you know it) Advertising Age piece.
The concept of do not track has not been endorsed by the commission or, in my judgment, even properly vetted yet. In actuality, in a preliminary staff report issued in December 2010, the FTC proposed a new privacy framework and suggested the implementation of do not track. The commission voted to issue the preliminary FTC staff report for the sole purpose of soliciting public comment on these proposals. Indeed, far from endorsing the staff’s do-not-track proposal, one other commissioner has called it premature.
Do-Not-Track does need more vetting and consideration. Don’t get your hopes up about being free of tracking anytime soon. (Do you even know what “tracking” is?)
If Do-Not-Track goes forward, don’t get your hopes up to be free of tracking either. When you take control of what your browser sends out over the Internet?
Then you can rightly anticipate being free of unwanted tracking!
 Last night, Declan McCullagh of CNet posted two tweets related to the concerns already percolating in the privacy community about a new Apple and Android app called “Color,” which allows those who use it to take photos and videos and instantaneously share them with other people within a 150-ft radius to create group photo/video albums. In other words, this new app marries photography, social networking, and geo-location.
Last night, Declan McCullagh of CNet posted two tweets related to the concerns already percolating in the privacy community about a new Apple and Android app called “Color,” which allows those who use it to take photos and videos and instantaneously share them with other people within a 150-ft radius to create group photo/video albums. In other words, this new app marries photography, social networking, and geo-location.  And because the app’s default setting is to share every photo and video you snap openly with the world, Declan wonders “How long will it take for the #privacy fundamentalists to object to Color.com’s iOS/Android apps?” After all, he says facetiously, “Remember: market choices can’t be trusted!” He then reminds us that there’s really nothing new under the privacy policy sun and that we’ve seen this debate unfold before, such as when Google released its GMail service to the world back in 2004.
And because the app’s default setting is to share every photo and video you snap openly with the world, Declan wonders “How long will it take for the #privacy fundamentalists to object to Color.com’s iOS/Android apps?” After all, he says facetiously, “Remember: market choices can’t be trusted!” He then reminds us that there’s really nothing new under the privacy policy sun and that we’ve seen this debate unfold before, such as when Google released its GMail service to the world back in 2004.
Indeed, for me, this debate has a “Groundhog Day” sort of feel to it. I feel like I’ve been fighting the same fight with many privacy fundamentalists for the past decade. The cycle goes something like this: Continue reading →




 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.