Articles by Adam Thierer 
 Senior Fellow in Technology & Innovation at the R Street Institute in Washington, DC. Formerly a senior research fellow at the Mercatus Center at George Mason University, President of the Progress & Freedom Foundation, Director of Telecommunications Studies at the Cato Institute, and a Fellow in Economic Policy at the Heritage Foundation.
Senior Fellow in Technology & Innovation at the R Street Institute in Washington, DC. Formerly a senior research fellow at the Mercatus Center at George Mason University, President of the Progress & Freedom Foundation, Director of Telecommunications Studies at the Cato Institute, and a Fellow in Economic Policy at the Heritage Foundation.
 Berin recently encouraged me to re-read Thomas Sowell’s The Vision of the Anointed: Self-Congratulation as a Basis for Social Policy, which I hadn’t looked at since I first read it back in 1995 or 96. I’m glad I did since Sowell’s work has always been profoundly influential on my thinking (especially his masterpiece, A Conflict of Visions) and I had forgotten how useful The Vision of the Anointed was in helping me understand the reoccurring model that drives ideological crusades to expand government power over our lives and economy.
Berin recently encouraged me to re-read Thomas Sowell’s The Vision of the Anointed: Self-Congratulation as a Basis for Social Policy, which I hadn’t looked at since I first read it back in 1995 or 96. I’m glad I did since Sowell’s work has always been profoundly influential on my thinking (especially his masterpiece, A Conflict of Visions) and I had forgotten how useful The Vision of the Anointed was in helping me understand the reoccurring model that drives ideological crusades to expand government power over our lives and economy.
“The great ideological crusades of the twentieth-century intellectuals have ranged across the most disparate fields,” Sowell noted in the book. But what they all had in common, he argued, was “their moral exaltation of the anointed above others, who are to have their different views nullified and superseded by the views of the anointed, imposed via the power of government.” (p. 5) These elitist, government-expanding crusades shared several key elements, which Sowell identified as follows:
- Assertion of a great danger to the whole society, a danger to which the masses of people are oblivious.
- An urgent need for government action to avert impending catastrophe.
- A need for government to drastically curtail the dangerous behavior of the many, in response to the prescient conclusions of the few.
- A disdainful dismissal of arguments to the contrary as either uninformed, irresponsible, or motivated by unworthy purposes.
You can see this model at work on a daily basis today with our government’s various efforts to reshape our economy, but I think this model is equally applicable to debates over social policy and speech control. In particular, the various “technopanics” I have been writing about recently fit this model. (See 1, 2, 3, 4, 5). For example, consider how this plays out in the debate over online social networking:
Continue reading →
As Berin mentioned last week, we have a new paper out on proposals to expand the Children’s Online Privacy Protection Act (COPPA) of 1998. We generically refer to those COPPA-expansion efforts as “COPPA 2.0.” Hence, the title of our paper: “COPPA 2.0: The New Battle over Privacy, Age Verification, Online Safety & Free Speech.” To recap what Berin already noted, in the name of improving online child safety, some legislators and state attorneys general (AGs) are advocating the expansion of COPPA’s “verifiable parental consent” model of age verification before certain sites or services may collect, or enable the sharing of, personal information for children.
Unlike “COPPA 1.0,” however, which only applied to children under the age of 13, “COPPA 2.0” would apply to all minors up to age 17. Moreover, the range of sites covered by the new law would generally be expanded to include just about any site or service with social networking functionality.
Since Berin has already summarized our general concerns with efforts to expand COPPA’s “verifiable parental consent” online age verification system to cover more online users and sites, I thought I would focus here on what I believe will be the most controversial (and important) part of our paper — our discussion about how COPPA 2.0 affects the speech rights of both adults
and adolescents.
Continue reading →
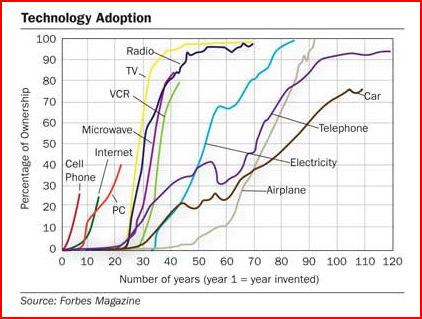
Via Kevin Kelly I see that at some point Forbes magazine produced this chart measuring technology diffusion rates for various media and communications technologies since their year of inception.
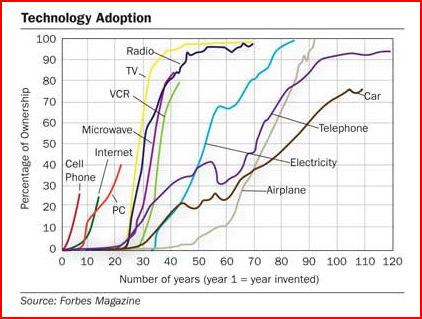 I found this of great interest because, since the mid-90s, I have been putting together various charts and tables illustrating technological diffusion [most recently I did this in my “Media Metrics” report] and this particular chart is quite challenging since you are forced to pick a “Year 1” date to begin each of the “S curves.” For example, what is “Year 1” for electricity or telephony on one hand, or the PC or the Internet on the other? That’s not always easy to determine since it is unclear when certain technologies were “born.”
I found this of great interest because, since the mid-90s, I have been putting together various charts and tables illustrating technological diffusion [most recently I did this in my “Media Metrics” report] and this particular chart is quite challenging since you are forced to pick a “Year 1” date to begin each of the “S curves.” For example, what is “Year 1” for electricity or telephony on one hand, or the PC or the Internet on the other? That’s not always easy to determine since it is unclear when certain technologies were “born.”
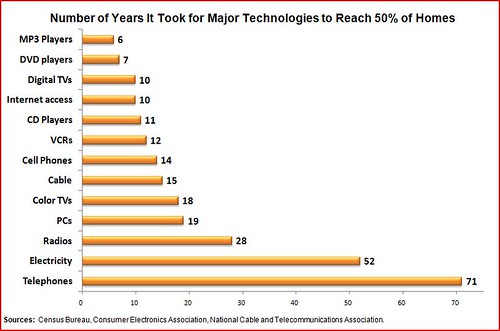
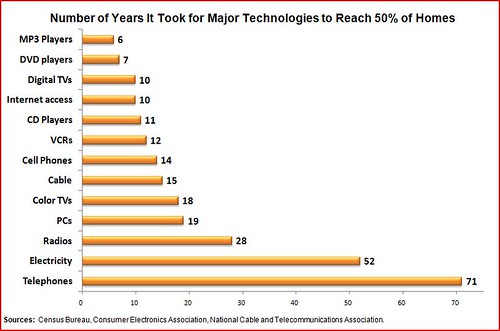
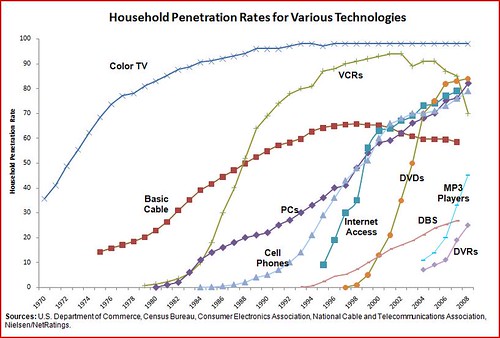
Regardless, no matter how you cut it, the more modern and the less regulated the technologies, the quicker they get to market. Here’s a couple of my recent charts illustrating that fact. The first shows how long it took before various technologies reached 50% household penetration. The second illustrates the extent of household diffusion over time.
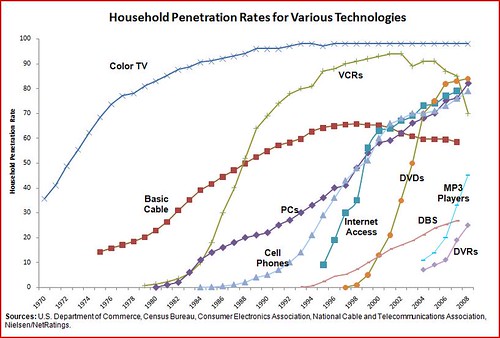 However, as Kevin Kelly notes, we usually never see any technology hit 100% household penetration (although the boob tube got close!):
Continue reading →
However, as Kevin Kelly notes, we usually never see any technology hit 100% household penetration (although the boob tube got close!):
Continue reading →
I’m reading a couple of interesting books right now [see my Shelfari list here] including Guarding Life’s Dark Secrets: Legal and Social Controls over Reputation, Propriety, and Privacy by Lawrence Friedman of the Stanford School of Law. The book examines the legal and social norms governing privacy, reputation, sex, and morals over the past two centuries. It’s worth putting on your reading list. [Here’s a detailed review by Neil Richards.] I might pen a full review later but for now I thought I would just snip this passage from the concluding chapter:
In an important sense, privacy is a modern invention. Medieval people had no concept of privacy. They also had no actual privacy. Nobody was ever alone. No ordinary person had private space. Houses were tiny and crowded. Everyone was embedded in a face-to-face community. Privacy, as idea and reality, is the creation of a modern bourgeois society. Above all, it is a creation of the nineteenth century. In the twentieth century it became even more of a reality. [p. 258]
In a time when amorphous “rights” to privacy seem to be multiplying like wildflowers, this is an important insight from Friedman. In my opinion, many of the creative privacy theories being concocted today are often based on false nostalgia about some forgotten time in the past when we supposedly all had our own little quiet spaces that were completely free from privacy intrusions. But as Friedman makes clear, this is largely a myth. It’s not to say that there aren’t legitimate issues out there today. But it’s important that we place modern privacy issues in a larger historical context and understand how many of today’s concerns pale in comparison to the problems of the past.
[Note: If you’re interested in this topic, you’ll also want to read Daniel Solove’s The Future of Reputation: Gossip, Rumor, and Privacy on the Internet. Also, here’s Jim Harper’s review of it.]
 California has asked the Supreme Court to review a Ninth Circuit Court of Appeals decision holding that a California video game statute was unconstitutional. [Game Politics.com has complete coverage, and there’s more over at Ars and USA Today’s Game Hunters blog.]
California has asked the Supreme Court to review a Ninth Circuit Court of Appeals decision holding that a California video game statute was unconstitutional. [Game Politics.com has complete coverage, and there’s more over at Ars and USA Today’s Game Hunters blog.]
Brief background: In late February, the Ninth Circuit upheld an August 2007 ruling by a California district court decision in the case of
Video Software Dealers Association v. Schwarzenegger [decision here], which struck down a California law, passed in October 2005 (A.B.1179), which would have blocked the sale of “violent” video games to those under 18 and required labels on all games. Offending retailers could have been fined for failure to comply with the law. After being challenged by the Video Software Dealers Association and the Entertainment Software Association and, the district court blocked the law arguing that it violated both the First and Fourteenth Amendments to the federal Constitution.
California’s decision to appeal the law up to the Supreme Court [petition is here] sets up a potential historic First Amendment decision (if they Court agrees to take the case, that is). California is asking the Court to consider two questions:
1. Does the First Amendment bar a state from restricting the sale of violent video games to minors?
2. If the First Amendment applies to violent video games that are sold to minors, and the standard of review is strict scrutiny, under Turner Broadcasting System, Inc. v. F.C.C., 512 U.S. 622, 666 (1994), is the state required to demonstrate a direct causal link between violent video games and physical and psychological harm to minors before the state can prohibit the sale of the games to minors?
California is essentially asking the Supreme Court to engage in a constitutional revolution and upset a century’s worth of First Amendment jurisprudence.
Continue reading →
As I mentioned in a post last month, dozens of comments were filed with the Federal Communications Commission (FCC) as part of the agency’s “Child Safe Viewing Act” Notice of Inquiry. Again, this proceeding was required under the “Child Safe Viewing Act of 2007,” which Congress passed last year and President Bush signed last December. The goal of the bill and the FCC’s proceeding (MB 09-26) is to study “advanced blocking technologies” that “may be appropriate across a wide variety of distribution platforms, including wired, wireless, and Internet platforms.” I filed 150+ pages worth of comments in this matter, and here’s my analysis of why this bill and the FCC’s proceeding are worth monitoring closely.
Anyway, this week saw many of the same groups that filed before (and some new ones) file reply comments about those earlier submissions. To make things simple, I have collected most of the notable reply comments down below in case anyone is interested.
Continue reading →
As part of our ongoing series that tracks the gradual transition of video content to the boob tube to online outlets, I want to draw everyone’s attention to two excellent articles in today’s Washington Post about this trend. One is by Paul Fahri (“Click, Change: The Traditional Tube Is Getting Squeezed Out of the Picture“) and the other by Monica Hesse (“Web Series Are Coming Into A Prime Time of Their Own“). I love the way Paul opens his piece with a look forward at how many of us will be explaining the “old days” of TV viewing to our grand kids:
S
it down, kids, and let Grandpa tell you about something we used to call “watching television.”
Why, back when, we had to tune to something called a “channel” to see our favorite programs. And we couldn’t take the television set with us
; we had to go see it!
Ah, those were simpler times.
Oh, sure, we had some technology we thought was pretty fancy then, too, like your TiVo and your cable and your satellite, which gave us a few hundred “channels” of TV at a time. Imagine that — just a few hundred! And we had to pay for it every month! Isn’t the past quaint, children?
Well, it all started to change around aught-eight, or maybe ’09, for sure. That’s when you no longer needed a television to watch all the television you could ever want.
Yes, I still remember it like it was yesterday . . .
Too true. Anyway, Paul goes on to document how some folks have already completely made the jump to an online-online TV existence and are doing just fine, although the idea of us all gathering around the tube to share common experiences may be a causality of the migration to smaller screens, he notes.
Continue reading →
As faithful readers no doubt know, I’m a big fan of Section 230 and believe it has been the foundation of a great many of the online freedoms we enjoy (dare I say, take for granted?) today. That’s why I’m increasingly concerned about some of the emerging thinking and case law I am seeing on this front, which takes a decidedly anti-230 tone.
Consider, for example, how some might weaken Sec. 230 in the name of “child safety.” You will recall the friendly debate about the future of Sec. 230 that I engaged in with Harvard’s John Palfrey. Prof. Palfrey has argued that: “The scope of the immunity the CDA provides for online service providers is too broad” and that the law “should not preclude parents from bringing a claim of negligence against [a social networking site] for failing to protect the safety of its users.” Similarly, Andrew LaVallee of The Wall Street Journal reported from a conference this week that Sec. 230 became everyone’s favorite whipping boy, with several participants suggesting that the law needs to be re-opened and altered to somehow solve online “cyber-bullying” problems.
Continue reading →
Building on this week’s Cato Unbound online debate over the impact of Lawrence Lessig’s Code ten years after it’s release, Tim Lee has posted a terrific essay over at the Freedom to Tinker Blog “Sizing Up “Code” with 20/20 Hindsight.” Tim concludes:
It seems to me that the Internet is rather less malleable than Lessig imagined a decade ago. We would have gotten more or less the Internet we got regardless of what Congress or the FCC did over the last decade. And therefore, Lessig’s urgent call to action — his argument that we must act in 1999 to ensure that we have the kind of Internet we want in 2009 — was misguided. In general, it works pretty well to wait until new technologies emerge and then debate whether to regulate them after the fact, rather than trying to regulate preemptively to shape the kinds of technologies that are developed.
As I wrote a few months back, I think Jonathan Zittrain’s The Future of the Internet and How to Stop It makes the same kind of mistake Lessig made a decade ago: overestimating regulators’ ability to shape the evolution of new technologies and underestimating the robustness of open platforms. The evolution of technology is mostly shaped by engineering and economic constraints. Government policies can sometimes force new technologies underground, but regulators rarely have the kind of fine-grained control they would need to promote “generative” technologies over sterile ones, any more than they could have stopped the emergence of cookies or DPI if they’d made different policy choices a decade ago.
I agree whole-heartedly, of course, and this is the point I was trying to make in my in my first essay in the Cato debate when I argued:
Lessig’s lugubrious predictions proved largely unwarranted. Code has not become the great regulator of markets or enslaver of man; it has been a liberator of both. Indeed, the story of the past digital decade has been the exact opposite of the one Lessig envisioned in Code. Cyberspace has proven far more difficult to “control” or regulate than any of us ever imagined. More importantly, the volume and pace of technological innovation we have witnessed over the past decade has been nothing short of stunning.
Anyway, read Tim’s entire essay.
I’ve posted another response in the Cato Unbound online debate over the impact of Lawrence Lessig’s Code and Other Laws of Cyberspace upon the book’s 10th anniversary. You will recall that I went fairly hard on Prof. Lessig in my essay, “Code, Pessimism, and the Illusion of ‘Perfect Control,’” and Lessig responded with a counter-punch that went after me for it. I respond in a new essay about “Our Conflict of Cyber-Visions.” In the piece, I address Lessig’s assertion that I just didn’t understand the central teachings of Code, as well as his reluctance to accept the “cyber-collectivism” label that I affixed to his book and life’s work. Again, please hop over to Cato Unbound for my complete response.
But one thing from the essay that I thought worth reproducing here is my effort to better define the key principles that separate the cyber-libertarian and cyber-collectivist schools of thinking. I argue that it comes down to this:
The cyber-libertarian believes that “code failures” are ultimately better addressed by voluntary, spontaneous, bottom-up, marketplace responses than by coerced, top-down, governmental solutions. Moreover, the decisive advantage of the market-driven approach to correcting code failure comes down to the rapidity and nimbleness of those response(s).
Of course, another key difference relates to how quickly one jumps to the conclusion that “code failures” are actually occurring at all. I argue:
Continue reading →
 Berin recently encouraged me to re-read Thomas Sowell’s The Vision of the Anointed: Self-Congratulation as a Basis for Social Policy, which I hadn’t looked at since I first read it back in 1995 or 96. I’m glad I did since Sowell’s work has always been profoundly influential on my thinking (especially his masterpiece, A Conflict of Visions) and I had forgotten how useful The Vision of the Anointed was in helping me understand the reoccurring model that drives ideological crusades to expand government power over our lives and economy.
Berin recently encouraged me to re-read Thomas Sowell’s The Vision of the Anointed: Self-Congratulation as a Basis for Social Policy, which I hadn’t looked at since I first read it back in 1995 or 96. I’m glad I did since Sowell’s work has always been profoundly influential on my thinking (especially his masterpiece, A Conflict of Visions) and I had forgotten how useful The Vision of the Anointed was in helping me understand the reoccurring model that drives ideological crusades to expand government power over our lives and economy.

 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
Reply Comments in FCC’s “Child Safe Viewing Act” Notice of Inquiry
by Adam Thierer on May 20, 2009 · 17 comments
As I mentioned in a post last month, dozens of comments were filed with the Federal Communications Commission (FCC) as part of the agency’s “Child Safe Viewing Act” Notice of Inquiry. Again, this proceeding was required under the “Child Safe Viewing Act of 2007,” which Congress passed last year and President Bush signed last December. The goal of the bill and the FCC’s proceeding (MB 09-26) is to study “advanced blocking technologies” that “may be appropriate across a wide variety of distribution platforms, including wired, wireless, and Internet platforms.” I filed 150+ pages worth of comments in this matter, and here’s my analysis of why this bill and the FCC’s proceeding are worth monitoring closely.
Anyway, this week saw many of the same groups that filed before (and some new ones) file reply comments about those earlier submissions. To make things simple, I have collected most of the notable reply comments down below in case anyone is interested. Continue reading →