GamePolitics.com reports on a murder trial in Alabama in which the attorney for a disturbed teenager is blaming video games for his barbaric behavior:
The lawyer for a man being tried for murder is trying to convince an Alabama jury that the defendant believed he was acting out a video game when he murdered an 80-year-old man on Halloween, 2005.
As reported by the Decatur Daily, Andrew Reid Lackey, 24, does not dispute that he stabbed, shot and gouged out the eye of his victim, Charlie Newman. However, Lackey’s attorney, Randy Gladden, is pointing the finger at video games. From the newspaper report:
Actions that led to a deadly confrontation between a defendant and an 80-year-old widower resembled a video game to the accused… [Attorney] Gladden described Lackey… as a computer geek who had immersed himself in video games and lived in “a different world than you and I.”
Tapes of a 911 call made by the victim during the fatal confrontation, however, indicate that old-school greed may have been the motive. Lackey is heard to demand of the victim, ”Where’s the vault?” seven different times. Charlie Newman’s grandson had previously told Lackey that the victim kept a large sum of money in a vault under the stairs. However, no such vault existed.
It’s just disgraceful–but perhaps not all that surprising–that this desperate defense attorney would employ tactics like this. Video games have become the universal excuse
du jour for violent behavior. It’s absurd for all the reasons I have pointed out here before. It’s abundantly clear that old fashion greed and a disturbed mind motivated this particular crime, and if you think that sort of thing didn’t happen before video games came along, then you just haven’t read any history. Of course, they instead just blamed movies, comics, and books for the crimes back then! There’s always someone else or something else to blame. It’s the never-ending search for a universal scapegoat for irrational or criminal behavior. The twisted logic = Don’t blame the individual, blame the media.
Pathetic.
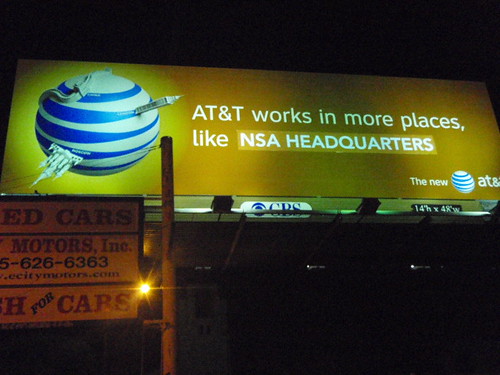
Despite the similarity in our names, I’m afraid we at TLF can’t take credit for the Billboard Liberation Front’s prank on AT&T. I’m normally a stickler for property rights, but I can’t get too worked up about this:
AT&T initially downplayed its heroic efforts in the War on Terror, preferring to serve in silence behind the scenes. “But then we realized we had a PR win on our hands,” noted AT&T V.P. of Homeland Security James Croppy. “Not only were we helping NSA cut through the cumbersome red tape of the FISA system, we were also helping our customers by handing over their e-mails and phone records to the government. Modern life is so hectic – who has time to cc the feds on every message? It’s a great example of how we anticipate our customers’ needs and act on them. And, it should be pointed out, we offered this service free of charge.”
Commenting on the action, and responding to questions about pending privacy litigation and the stalled Congressional effort to shield the telecoms from these lawsuits, NSA spokesperson [REDACTED] remarked: “[REDACTED] we [REDACTED] condone [REDACTED] warrantless [REDACTED], [REDACTED] SIGINT intercepts, [REDACTED] torture [REDACTED] information retrieval by [REDACTED] means necessary.”
Hat tip: Brian Doherty via Julian
I really enjoyed attending the Collective Intelligence FOO Camp, sponsored by Google and O’Reilly Media, last weekend. I’d been expecting a sort of geek slumber party, and had looked forward to rolling out my awesome Darth Vader impersonation. I was all set to cut loose with a growling, “I’m your father, Luke.” It didn’t quite come to that, but I still had a blast, meeting lots of smart, informed, articulate, creative, and successful people. Friendly people, too.
I described how to establish the legality of real money, open-access prediction markets under U.S. law. I called my presentation,
Getting from Collective Intelligence to Collective Action [PPT file]. In very brief, I proposed this algorithm:
- Set up an enterprise prediction market, make playing it a condition of continued employment, and offer valuable prizes to the best predictors.
- Set up a limited access prediction market, hire a number of independent contractors researchers to play it, pay them a relatively low salary for doing so, and offer valuable prizes to the best predictors.
- Set up an open-access prediction market but require anyone playing it to go through a click-wrap license that creates the sort of independent researcher relationship described at step 2, above.
Continue reading →
This account of the FCC’s Boston meeting on Comcast’s network management policies, from Tom Giovannetti.
Somewhere, there are more sophisticated arguments for net neutrality:
The setting where a monopoly infrastructure business, in pursuit of its own ends, could take arbitrary steps that would ruin one business and make another succeed, were regarded as inimical to a really free market. It resembled far too much the widely disliked markets without property rights, dominated by a capricious political power. So what followed was a long period of increasingly stringent regulation.
One might conclude from this discussion of historical precedents for regulation of networks that something like network neutrality ought to be attempted. My take in brief is that that Andrew’s paper understates the aspects of the cure that are worse than the disease and neglects the history of networks beyond a simple pricing story. It is time to try another approach. But there could be some interesting discussion.
Interestingly, though, the current trend in the Comcast proceeding bears no resemblance to a reasoned attempt to provide a real solution to any real problem, to consider the history of networks, or to consider a range of solutions and their tradeoffs. It seems to be an exercise in pure faddish populism. Curious. One wonders what a court will make of it. Mincemeat, I suspect.
The Berkman Center for Internet & Society at Harvard Law School has just announced the formation of the Internet Safety Technical Task Force, and they were kind enough to ask me to serve as a member. According to the press release they sent out this morning:
The Task Force will evaluate a broad range of existing and state-of-the-art online safety technologies, including a review of identity authentication tools to help sites enforce minimum age requirements. The Task Force is a central element of the Joint Statement on Key Principles of Social Networking Safety announced in January 2008 by MySpace and the Attorneys General Multi-State Working Group on Social Networking. Fifty Attorneys General adopted the “Joint Statement” with the goal of improving online safety standards industry-wide.
[I discussed the details of that My Space-AG “joint statement in this report back in January.] The Task Force is composed of industry-leading Internet businesses, non-profit organizations, and technology companies, including: AOL, Aristotle, AT&T, Bebo, Center for Democracy & Technology, Connectsafely.org, Comcast, Enough is Enough, Facebook, Google, the Family Online Safety Institute, iKeepSafe, the Institute for Policy Innovation, Linden Lab, Loopt, IDology, Microsoft, MySpace, NCMEC, Progress and Freedom Foundation, Sentinel Tech, Symantec, Verizon, WiredSafety.org, Xanga, and Yahoo! The Task Force will be chaired by John Palfrey, executive director of the Berkman Center.
Over the past year, I have been very active on many of the issues that will be at the core of the task force’s mission, including the identify authentication / age verification debate. For those who might be interested, I’ve included the relevant PFF studies and links down below the fold. I’m looking forward to working with the other members of the Task Force to conduct a comprehensive review of these issues. I’m sure I will be reporting here occasionally on our progress.
Continue reading →
As I mentioned way back in 2005, the specter of FCC content controls for cell phone and other mobile media devices is growing. And, according to this new Radio Ink report, it’s now under serious consideration at the FCC:
FCC Commissioner Deborah Taylor Tate says the FCC is looking into how its indecency regulations could extend to the increasing availability of audio and video content delivered to mobile devices. In a recent speech delivered at the Association of National Advertisers Advertising Law and Business Affairs Conference, Tate said, “As we enter the age of content delivery over mobile devices, there is a whole new set of questions to address regarding how to provide ratings, how to block objectionable content, and whether the FCC has a role to play in this arena.”
To be fair, Commissioner Tate also praised the voluntary steps that industry has already taken to empower parents to deal with this privately. And Tate also said that, “market-based solutions are the best way to achieve our shared goals and to provide parents the tools they need to be the first line of defense for their children.” But the threat of more aggressive intervention by the FCC still looms in light of her earlier comments. Stay tuned; much more to come on this front.
Dominance in the broadband market is a battle of both technology and politics. Right now Comcast, America’s leading cable company, is losing on both counts.
Comcast Executive Vice President David Cohen emerged from the Federal Communications Commission’s hearing on Internet practices in Cambridge, Mass., as unable to defend himself and his company against charges of blocking the peer-to-peer (P2P) Internet application BitTorrent.
Comcast also came out looking like the kind of bullying corporation that resorts to packing the auditorium with its own employees.
Besides, Comcast is not a very good FOK, or Friend of Kevin — as in Kevin Martin, the chairman of the agency. Martin has done nearly everything in his power to harm Comcast and the cable industry since he took over the FCC in March 2005.
Continue reading →
The Federal Communications Commission conducted a public hearing this week on network management before a group of law students – as opposed to, say, engineering students who are the ones who study network management – where lead witness Rep. Ed Markey (D-MA) declared
[T]he Internet is as much mine and yours as it is Verizon’s, AT&T’s or Comcast’s. Please keep front and center in your examination the needs and wishes of the community of users rather than a small coterie of carriers.
As a matter of law, Markey would have flunked if that were an exam question. But of course the government has a right to try to control whatever it wishes one way or another.
The interesting and relevant question is whether and to what degree it’s possible to proscribe network management practices which most reasonable people would consider inappropriate without unintentionally preventing network providers from trying to improve their services while earning a competitive return on their investment.
“[C]learly, complicated network architectures, Internet viruses, and capacity limitations raise real-world, complex and valid questions, conceded FCC Commissioner Michael J. Copps. “Our job is to figure out when and where you draw the line between discrimination and reasonable network management.”
Continue reading →
Tom Bell–who I regarded as the the equivalent of my Jedi master in the mid-90s–suggested in a post earlier today that:
“Copyright holders thus understandably fear that their customers have begun to treat expressive works like common property, free for all to use. That, the specter of copyism, does risk upsetting copyright policy, leading to a market failure in the production of expressive works. Even as we recognize that threat, however, we should also appreciate that technological advances have greatly reduced the costs of creating and distributing new works of authorship. Thanks to that deflation, we can increasingly count on authors who care little about the lucre of copyright — blockheads, as Samuel Johnson called them — to supply us with original expressive works.”
As his once lowly Padawan learner, I know to be cautious when questioning my old master’s wisdom. But I must humbly ask: How, dear master, does a video game this frickin cool and complex get created in a world devoid of serious copyright protections? It’s a question I have asked before here and I have never received an answer that satisfied my fear of losing some of the truly great content that gets created only because of the protections afforded by existing copyright standards.
I await your enlightenment, my master. Because I can’t imagine many “blockheads” providing us with expressive works like this without some sort of guarantee that their creative efforts will not be completely expropriated.
http://image.com.com/gamespot/images/cne_flash/production/media_player/proteus/gs/proteus_embed.swf
[More videos of “Star Wars: The Force Unleashed” can be found here.]

 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.