Three rings for the broadcast-kings filling the sky,
Seven for the cable-lords in their head-end halls,
Nine for the telco-men doomed to die,
One for the White House to make its calls
On Capitol Hill where the powers lie,
One ring to rule them all, one ring to find them,
One ring to bring them all and without the Court bind them,
On Capitol Hill where the powers lie.
Myths resonate because they illustrate existential truths. In J.R.R. Tolkien’s mythical tale, the Lord of the Rings, the evil Lord Sauron imbued an otherwise very ordinary ring – the “One Ring”– with an extraordinary power: It could influence thought. When Sauron wore the One Ring, he could control the lords of the free peoples of Middle Earth through lesser “rings of power” he helped create. The extraordinary power of the One Ring was also its weakness: It eventually corrupted all who wore it, even those with good intentions. This duality is the central truth in Tolkien’s tale.
It is also central to current debates about freedom of expression and the Internet.
Since the invention of the printing press, those who control the means of mass communication have had the ability to influence thought. The printing press enabled the rapid and widespread circulation of ideas and information for the first time in history, including ideas that challenged the status quo (e.g., sedition and heresy). Governments viewed this new technology as a threat and responded by establishing control over the machinery of the printing press through state monopolies, press licenses, and special taxation.
“The right to think is the beginning of freedom, and speech must be protected from the government because speech is the beginning of thought.”
The Framers knew that freedom of expression is the foundation of freedom. They also recognized that governments could control thought by controlling the printing press, and included a clause in the First Amendment prohibiting government interference with the “freedom of the press.” Though this clause was aimed at the printing press, its protection is not limited to the mass communications media of the Eighteenth Century. The courts have held that the First Amendment encompasses new mass media technologies, including broadcast television and cable.
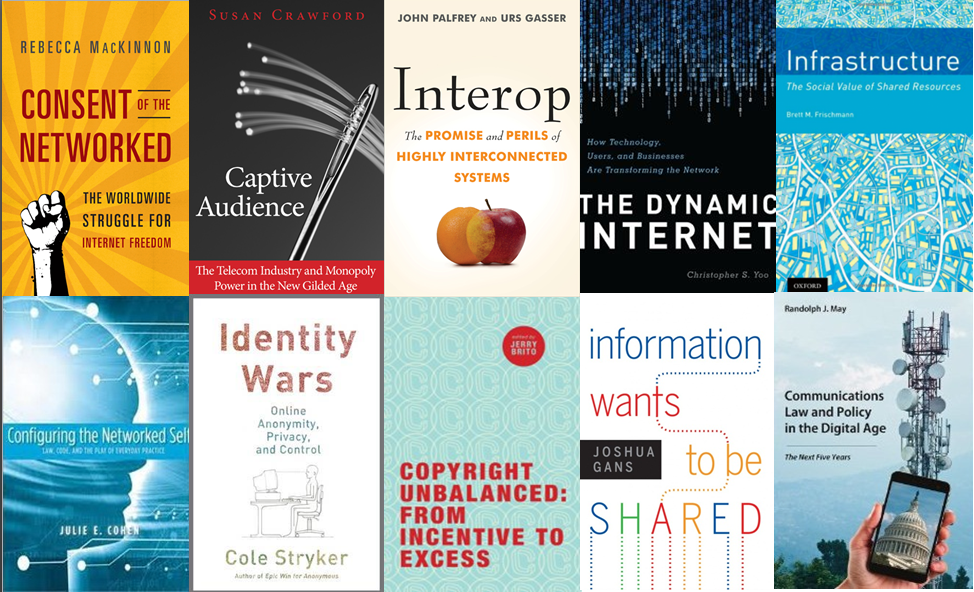
Several public interest groups, academics, and pundits across the political spectrum nevertheless argue that the latest mass communications technology – the Internet – does not merit protection from government interference on First Amendment grounds. They assert that neither the dissemination of speech by Internet service providers (ISPs) nor the results of Internet search engines (e.g., Google) are entitled to First Amendment protection. They fear that Internet companies will use the First Amendment to justify the exercise of editorial control over the free expression of their consumers.
Others (including the Competitive Enterprise Institute) argue that the First Amendment applies to bothISPs and search engines. They believe a government with unrestrained control over the means of mass communications has the incentive and the ability to use that power to control the thoughts of its people, which inevitably leads to authoritarianism. They point to Internet censorship by China, Syria, and other authoritarian governments as current proof of this principle.
Both sides in the Internet debate raise legitimate concerns. I suspect many consumers do not want ISPs and search engines to exercise unfettered control over the Internet. I suspect that just as many consumers do not want government to exercise unfettered control over the Internet either. How can we resolve these dual concerns?
The free peoples of Middle Earth struggled with a similar duality at the Council of Elrond, where they decided what should be done with the One Ring. “Why not use this ring?” wondered Boromir, a bold hero who had long fought the forces of Sauron and believed the ring could save his people. Aragorn, a cautious but no less valiant hero, abruptly answered that no one on the Council could safely wield it. When Elrond suggested that the ring must be destroyed, mutual distrust drove the Council to chaos. Order was restored only when Frodo, a hobbit with no armies to command and no physical power, volunteered for the dangerous task of destroying the ring.
The judicial branch is our Frodo. It has no armies to command and no physical power. It must rely on the willingness of others to abide by its decisions and their strength to enforce them. Like the peoples of Middle Earth who relied on Frodo, we rely on the courts to protect us from abuse of government power because the judicial branch is the least threatening to our liberty.
This is as true today as it was when the Constitution was signed. Changes in technology do not change the balance of power among our branches of government. As we have in the earlier eras of the printing press, broadcast television, and cable, we must trust the courts to apply the First Amendment to mass communications in the Internet era.
Providing ISPs and search engines with First Amendment rights would prevent dangerous and unnecessary government interference with the Internet while permitting the government to protect Internet consumers within Constitutional bounds. Although some advocates imply otherwise, application of the First Amendment to Internet companies would not preclude the government from regulating the Internet. The courts uphold regulations that limit freedom of expression so long as they are narrowly tailored to advance a compelling or substantial government interest.
We have always trusted the courts to balance the right to freedom of expression with other rights and governmental interests, and there is no reason to believe they cannot appropriately balance competing concerns involving the Internet. If the courts cannot be trusted with this task, no one can.
 When the smoke cleared and I found myself half caught-up on sleep, the information and sensory overload that was CES 2013 had ended.
When the smoke cleared and I found myself half caught-up on sleep, the information and sensory overload that was CES 2013 had ended.
 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.