A number of conservative blogs have picked up on reports that the Obama administration is looking to data mine users on social networking sites. Reports CNS News: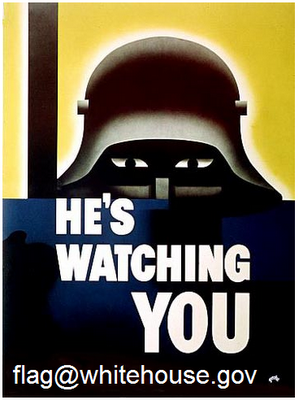
Anyone who posts comments on the White House’s Facebook, MySpace, YouTube and Twitter pages will have their statements captured and permanently archived by the federal government, according to a plan that the White House is now seeking a contractor to carry out.
Whenever government is collecting information about private citizens, we should be concerned. But this controversy smells a lot like privacy fear-mongering, even though it involves government. If you post a comment to an “official” Obama administration page on a social networking site, it seems only natural that it’s fair game for data mining. The same goes if you post a video response on a publicly accessible site.
If you’re posting controversial statements online under your real name for the public to see, what do you expect will happen? Anybody in the world who has an Internet connection can log your postings, so why shouldn’t government officials be able to do the same? Until government starts pressuring Facebook or Myspace to hand over data that’s being collected on an
involuntary basis, I don’t see a whole lot here to worry about.
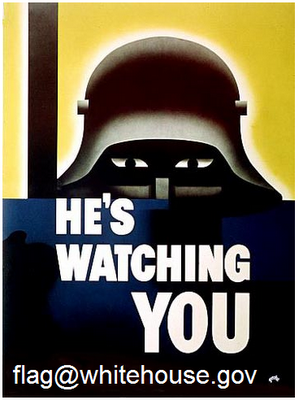
This controversy, and the flap over flag@whitehouse.gov from a few weeks back, raise another interesting question: should Congress reexamine the Presidential Records Act (PRA) of 1978? This is the law that governs Presidential record-keeping. According to some commentators, if the administration solicits data on its critics, it is obligated under the PRA to retain that data indefinitely. I haven’t read the law, but at first glance it appears that it may have some serious deficiencies. This is is hardly surprising, of course, given that the Internet — let alone social networks — didn’t even exist when the PRA was enacted in 1978.
Berin has already done a fine job tearing apart this latest effort by 10 activist groups to break the Internet by imposing burdensome regulation or punishing legal liability on Internet operators for the crime of trying to deliver relevant advertising to users that can actually pay for the content and services given away to users for free. To that, I would add my deep disappointment that the Electronic Freedom Foundation (EFF) choose to join this cabal. After all, the other members of the coalition are frequently heard calling for regulation of one variety or another. But EFF always prides itself on supposedly avoiding online regulatory schemes. That’s what makes it so surprising that they chose to jump on this bandwagon for an Internet industrial policy in the name of “protecting privacy.”
EFF’s embrace of regulation is particularly inconsistent given their excellent filing in the FCC’s “Child Safe Viewing Act” proceeding this summer. As I’ve previously noted, this proceeding raises the specter of “convergence-era content regulation” with Congress authorizing the FCC to look into “advanced blocking controls” for “wired, wireless, and Internet” platforms. EFF’s comments rightly stressed dangers of expanded content controls or Internet regulation, and noted the many “less-restrictive means” available to the public that provide compelling alternatives to government regulation: “Blocking technologies are widely available in the market and do not require further government support.” And EFF has been instrumental throughout the years of making the case in courts for applying the less-restrictive means test and strict scrutiny when it comes to government efforts to regulate speech.
Why, then, does EFF take the diametrically opposite position when privacy concerns enter the picture? Continue reading →
A coalition of ten self-described “consumer and privacy advocacy organizations” today demanded legislation that would restrict the collection and use of data online for customizing advertising based on Internet users’ interests. I’ll have more to say on this but here are my initial comments:
These so-called “consumer advocates” are actually anti-consumer elitists. Not only do they presume that consumers are too stupid or lazy to make their own decisions about privacy, but they ignore the benefits to consumers: more relevant advertising plus more and better content.
Advertising has been the “mother’s milk” of media in America since colonial times and the future of media depends on the ability of publishers to replicate that revenue model online. Micropayments, donations, subscriptions alone simply can’t fund a vibrant marketplace of ideas. Only personalized advertising can sustain publishers through the Digital Revolution.
Regulatory advocates haven’t demonstrated any harm to consumers that would justify such sweeping preemptive regulation. By strangling funding for new media, such regulations would amount to an “Industrial Policy” for the Internet. Instead, policymakers should focus on educating consumers and empowering them by promoting development of better privacy management tools.
According to a report by CNET’s Declan McCullagh, a draft bill in the U.S. Senate would grant President Obama “cybersecurity emergency powers” to disconnect and even seize control of private sector computers on the Internet.
Back in May, when Obama proposed a “cybersecurity czar with a broad mandate” and the administration issued a report outlining potential vulnerabilities in the government’s information security policies, I cautioned about the constant temptation by politicians in both parties to expand government authority over “critical’ private networks.” From American telecommunications to the power grid, virtually anything networked to some other computer would potentially be fair game for Obama to exercise “emergency powers.”
Policy makers should be suspicious of proposals to collectivize and centralize cybersecurity risk management, especially in frontier industries like information technology. When government asserts authority over security technologies, it hinders the evolution of more robust information security practices and creates barriers to non-political solutions—both mundane and catastrophic. The result is that we become less secure, not more secure.
Instead, the Obama Administration should limit its focus to securing government networks and keeping government agencies on the cutting edge of communications technology. As today’s news illustrates, the dangers created by such a broad mandate may come to pass.
Mediapost has published an interview I gave to Omar Tawakol, founder of the BlueKai registry entitled “User Empowerment, Not Regulation, Is The Answer to Privacy Concerns About Targeted Ads” in which I summarize the arguments Adam Thierer and I have been making since our “Principles to Guide the Debate” piece last September.
We argue for user empowerment over restrictive defaults (like “opt-in”) for data use and collection because, as the Supreme Court held in 2000: “Technology expands the capacity to choose; and it denies the potential of this revolution if we assume the Government is best positioned to make these choices for us.”
We promote tools that let users make their own decisions about privacy, not only because those decisions are fundamentally subjective, but because regulatory mandates could stifle the development of online content and commerce.
I also note the parallels between speech controls and privacy regulation, and call for a consistent, principled approach to both:
Since 1997, the Supreme Court has struck down multiple legislative attempts to censor online and offline content [especially the CDA] because there were “less restrictive alternatives” that would not so heavily burden free speech rights. In a 2000 cable-related decision, the Court held that “targeted blocking [by users] is less restrictive than banning, and the Government cannot ban speech if targeted blocking is a feasible and effective means of furthering its compelling interests.”
Courts have struck down other federal and state speech controls because parents had the tools to filter their kids’ access to information online, in video games, etc., as described in my PFF colleague Adam Thierer’s ongoing catalog of these tools…
Many who oppose industry self-regulation are not really “consumer advocates” because they don’t recognize that consumers have many, competing values. Those regulatory advocates are more interested in their preferred one-size-fits-all mandates than in empowering users to determine their own privacy preferences.
Like advocates of censorship, privacy zealots assert great dangers to which citizens are supposedly oblivious but which urgently require government intervention-dismissing arguments to the contrary as either uninformed or irresponsible.
The comments on the interview are equally worth reading. Jeff Chester, who has made a career out of attacking advertising, quickly posted a comment dismissing, but ignoring, my arguments about consumer welfare as corporate propaganda—just as he did with his comment on the post Adam and I wrote in June about congressional hearings on the issue featuring Chester (and Scott Cleland, the right-wing “Bizarro Chester“). I’ve had it with Chester’s ad hominem attacks on the motives of those who disagree with him, as I explained in my reply to Chester: Continue reading →
This clip from Fox News shows why more reporters need to contact the experts here at TLF:
http://www.youtube.com/v/mpDs1ii5n6w&hl=en&fs=1&color1=0x5d1719&color2=0xcd311b
The “security expert” being interviewed in the clip, Robert Siciliano, doesn’t seem to understand what cookies do. He claims that “cookies closest cousin is spyware.” Siciliano also implies that the Obama Administration might somehow be in league with Google to gather our private information.
I think there may be some valid concerns with cookies being implemented on certain government sites, but this sort of hyperbole only feeds into the baseless fears that already exist about technology.
I should note that Judge Andrew Napolitano provides some interesting analysis on the topic after the Siciliano interview, which is included in the clip.
Hat tip: dvorak.org/blog
. . . is not in doubt. But as technology advances, it will not be as strong an identifier as it has been up to now. Scientists have demonstrated that they can fabricate it.
I wrote about the qualities of identifiers – fixity, distinctiveness, and permanence – in my book
Identity Crisis. The ability to fabricate DNA renders it slightly less distinctive.
Jeff Jonas has published an important post: “Your Movements Speak for Themselves: Space-Time Travel Data is Analytic Super-Food!”
More than you probably realize, your mobile device is a digital sensor, creating records of your whereabouts and movements:
Mobile devices in America are generating something like 600 billion geo-spatially tagged transactions per day. Every call, text message, email and data transfer handled by your mobile device creates a transaction with your space-time coordinate (to roughly 60 meters accuracy if there are three cell towers in range), whether you have GPS or not. Got a Blackberry? Every few minutes, it sends a heartbeat, creating a transaction whether you are using the phone or not. If the device is GPS-enabled and you’re using a location-based service your location is accurate to somewhere between 10 and 30 meters. Using Wi-Fi? It is accurate below 10 meters.
The process of deploying this data to markedly improve our lives is underway. A friend of Jonas’ says that space-time travel data used to reveal traffic tie-ups shaves two to four hours off his commute each week. When it is put to full use, “the world we live in will fundamentally change. Organizations and citizens alike will operate with substantially more efficiency. There will be less carbon emissions, increased longevity, and fewer deaths.”
This progress is not without cost:
Continue reading →
 In a couple of blog posts on Cato@Liberty recently, I’ve used graphics to illustrate my very good points.
In a couple of blog posts on Cato@Liberty recently, I’ve used graphics to illustrate my very good points.
To sass the PR-ey use of Whitehouse.gov to advocate for health care regulation, and make a point or two about transparency, I modified the “Reality Check” image the White House created for their campaign. That was a good time.
But the
tour de force is the link that I embedded with a TSA graphic meant to illustrate what they’re doing with Secure Flight. For that one, you have to go look at the post. Read the graphic, enjoy its meaning, then do what it tells you to do.
 by Adam Thierer & Berin Szoka — (Ver. 1.0 — Summer 2009)
by Adam Thierer & Berin Szoka — (Ver. 1.0 — Summer 2009)
We are attempting to articulate the core principles of cyber-libertarianism to provide the public and policymakers with a better understanding of this alternative vision for ordering the affairs of cyberspace. We invite comments and suggestions regarding how we should refine and build-out this outline. We hope this outline serves as the foundation of a book we eventually want to pen defending what we regard as “Real Internet Freedom.” [Note: Here’s a printer-friendly version, which we also have embedded down below as a Scribd document.]
I. What is Cyber-Libertarianism?
Cyber-libertarianism refers to the belief that individuals—acting in whatever capacity they choose (as citizens, consumers, companies, or collectives)—should be at liberty to pursue their own tastes and interests online.
Generally speaking, the cyber-libertarian’s motto is “Live & Let Live” and “Hands Off the Internet!” The cyber-libertarian aims to minimize the scope of state coercion in solving social and economic problems and looks instead to voluntary solutions and mutual consent-based arrangements.
Cyber-libertarians believe true “Internet freedom” is freedom
from state action; not freedom for the State to reorder our affairs to supposedly make certain people or groups better off or to improve some amorphous “public interest”—an all-to convenient facade behind which unaccountable elites can impose their will on the rest of us.
Continue reading →




 The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.
The Technology Liberation Front is the tech policy blog dedicated to keeping politicians' hands off the 'net and everything else related to technology.